Deregistration
Description
The Nevis Mobile Authentication SDK also offers the option to deregister an authenticator from the device and the Nevis Mobile Authentication backend. To do this, the mobile application issues a single call to the SDK to trigger deregistration. The SDK requires that the user authenticates in-band. If the user verification is successful, it informs the backend about which authenticators are to be removed. The backend responds with a list of deleted authenticators, and all the related data that is stored locally on the device can also be removed.
It is possible that multiple authenticators used on multiple devices owned by the same user get deleted. This could happen with specific context modes used during the request to trigger deregistration. See the FIDO UAF Credential Deregistration chapter in the nevisFIDO documentation for more information.
Prerequisites
- The user performed a Registration first.
- The mobile application contains the Nevis Mobile Authentication SDK.
In-band deregistration
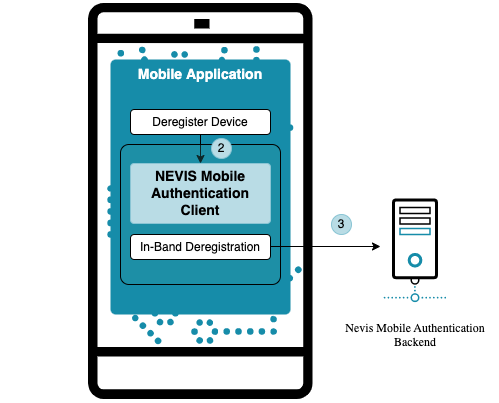
In-band deregistration is a FIDO deregistration that is initiated directly by the SDK that is integrated in the mobile application. The only communication channel involved is the one established between the SDK and the Nevis Mobile Authentication backend.
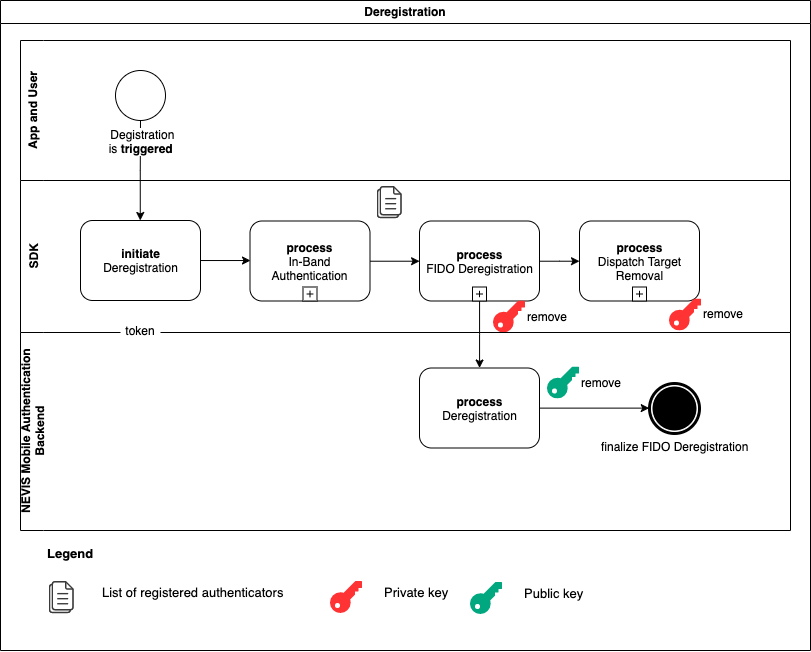
As opposed to other operations, where the backend is the master of the process, deregistration is initiated by the client and, the client functions as the master, telling the backend which credentials to remove.
In a realistic scenario, the backend is always configured to require authorization to carry out deregistration. The mobile application must pass an authenticated session, currently in the form of a cookie, to the SDK when initiating deregistration. To obtain a session of this type, the mobile application must first authenticate, for example, by providing a username and password, with the Nevis Mobile Authentication backend.
After successful authentication, the SDK removes the registered authenticators and dispatch target credentials. After this, the SDK informs the Nevis Mobile Authentication backend about the removed authenticators. In addition, it removes the dispatch target registration from the backend.
After successful completion of the operation, all of the private keys on the client side, as well as all of the public keys on the server side are removed.
FIDO deregistration
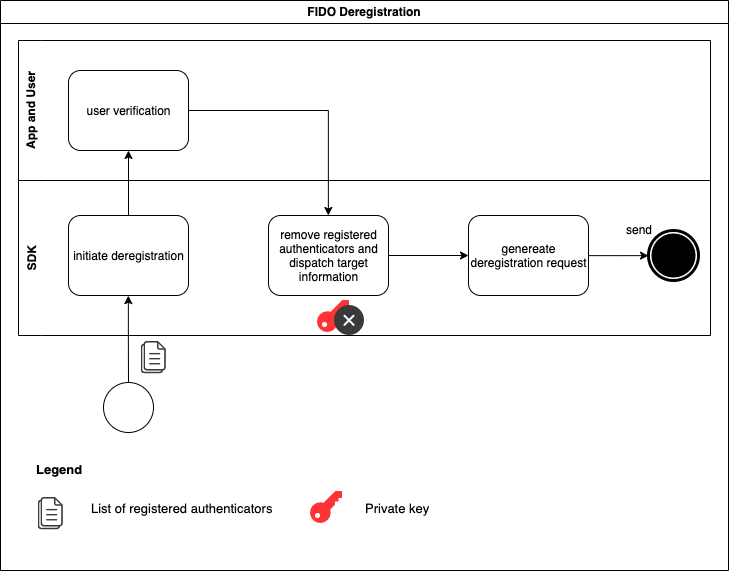
The SDK delegates to the app the responsibility of interacting with the user who needs to go through a verification process. The list of registered authenticators is used during this interaction. The app asks the user if they want to remove their device from the FIDO registration. After successful user verification, the SDK finalizes the FIDO deregistration process, creates a FIDO deregistration request, and sends it to the Nevis Mobile Authentication backend.