Multi-factor authentication
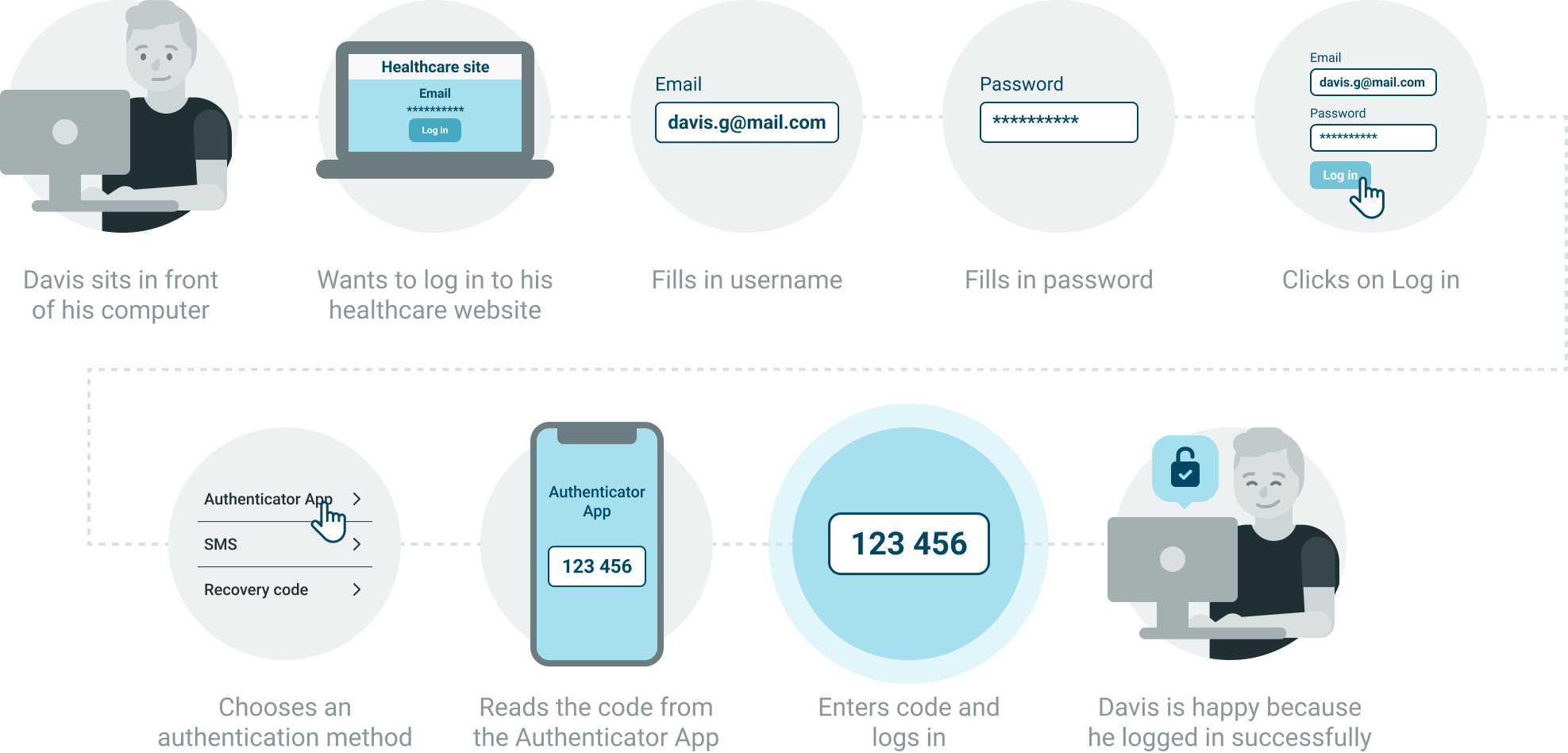
Multi-factor authentication provides another layer of authentication on top of logging in with a password.
Identity cloud supports the following second factors for Multi-factor authentication:
- Time-based-one-time password
- SMS
- Recovery codes
- Social login with
- Apple
- Microsoft
At least one of the authentication methods, Time-based-one-time password or SMS needs to be enabled as a second factor.
Recovery codes are always active as a fallback method and cannot be disabled.
If you enable multi-factor authentication, every user who only signed up with Social login needs to register a Password by going through the Password reset flow.
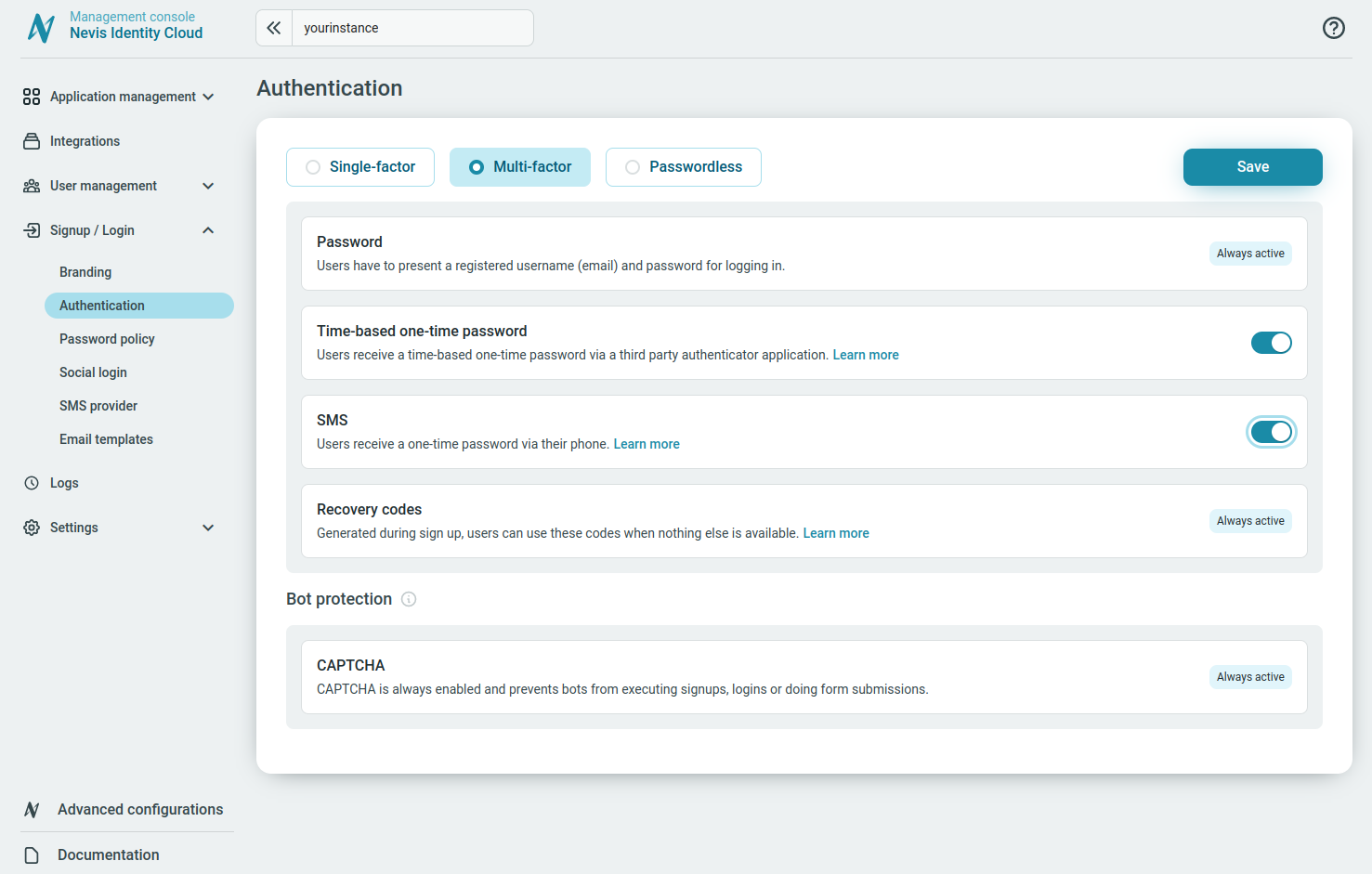
Password
By default, the Password authentication method is always active and used as the first authentication factor. For more information, see Password.
Time-based one-time password
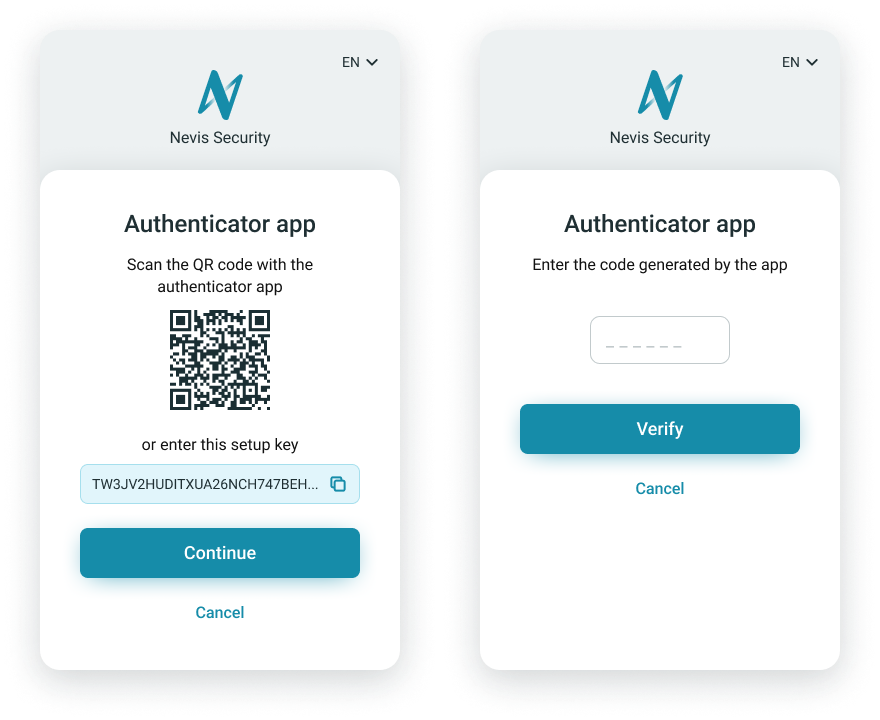
The method Time-base one-time password uses passwords generated by a third-party authenticator application for authentication of the users.
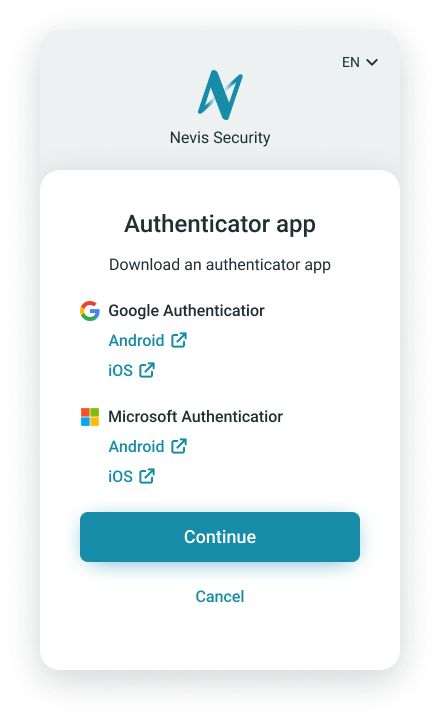
Users need an authenticator app such as Google Authenticator (App Store link, Play Store link), Microsoft (App Store link, Play Store link), or similar TOTP authenticator app to complete the authentication.
The Google Authenticator app can be downloaded from:
The Microsoft Authenticator app can be downloaded from:
Users can complete the authentication by doing either of the following:
- Scan the QR code with the authenticator app or copy-paste the setup key manually to set up the authenticator app.
- Enter the code generated by the app.
SMS
The SMS authentication method uses one-time passwords sent to the phones number of the users.
The users confirm the phone number to use for this type of authentication during the authentication method setup.
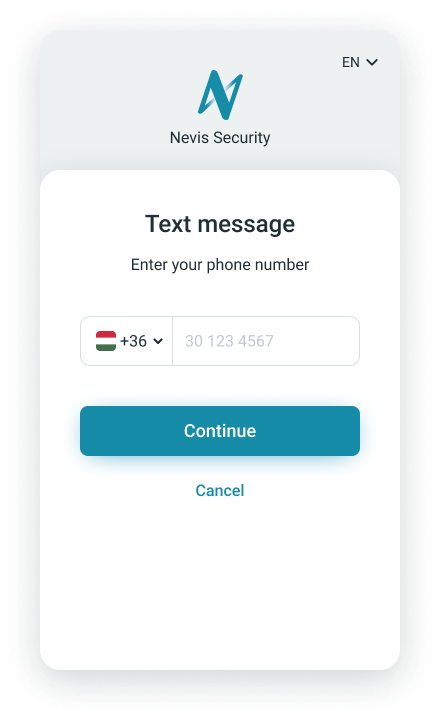
The phone number the users give for SMS verification does not need to match the Contact phone added to their Personal data.
The user receives a verification code to the provided phone number and is asked to enter it on the verification page.
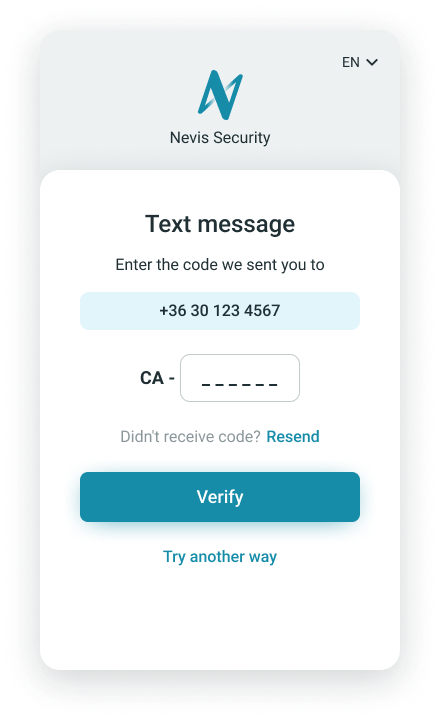
The successfully verified SMS authentication number appears under the Authentication methods tab of the user details view.
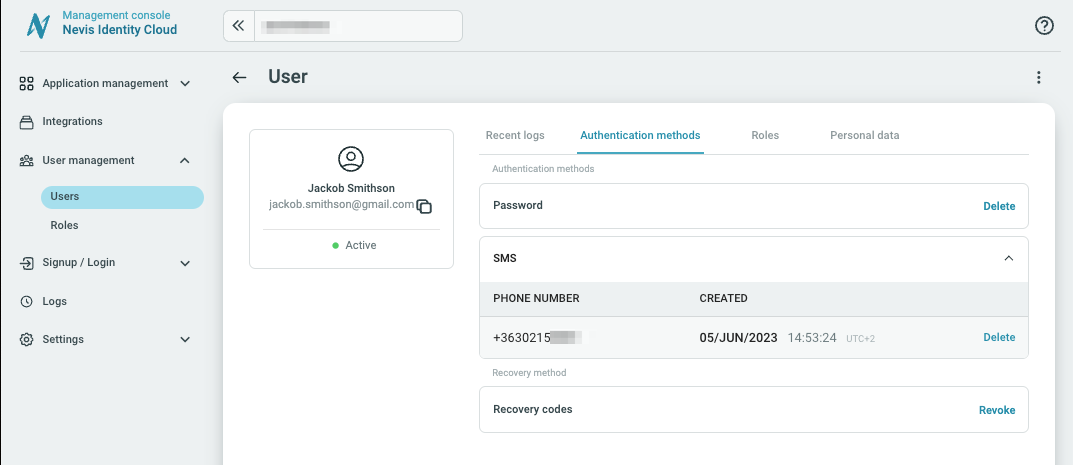
Before you can manage the authentication method SMS, you need to configure an SMS provider.
Changing the phone number for SMS verification
While the Contact phone number entered under Personal data can be modified, the phone number set up by the users for the SMS authentication method cannot be modified after initial registration.
Administrators can delete the SMS authentication method in the Management console. If a user does not have any second-factor authentication method besides recovery codes set up, then they can register a new phone number for the SMS authentication method during login after successful recovery codes authentication.
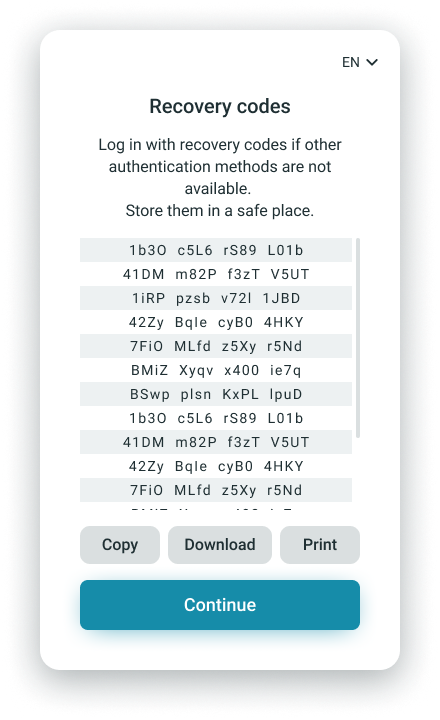
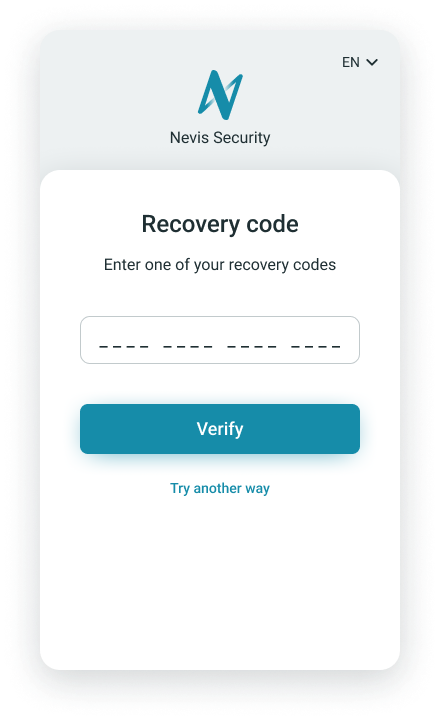
Recovery codes
The method Recovery codes uses 16 generated recovery codes to authenticate users. Each recovery code can only be used once. The Recovery codes can be copied, downloaded, or printed to store them in a safe place. A new set of recovery codes is automatically generated for a user after a completed login if all 16 recovery codes have been used.
The method Recovery codes is always active and cannot be disabled. The Recovery codes authentication method provides a fallback authentication method in case a user does not have access to phone or the authenticator app.
Social login
Social login is a federated authentication method using social identity providers to verify the user's identity. Read more about how social login works.
You can enable or disable the social login for each added social login provider. Toggling the option determines whether the social login button of the corresponding social identity provider is displayed on the signup and login pages.
Specifics of the authentication steps and supported account types may vary by social identity provider. For example, only business Microsoft accounts may be used to sign up and log in through Identity Cloud.
Add social login
Before you can manage the authentication method Social Login, you need to add and configure the corresponding social identity provider.
Disable social login
If you disable social login, every user who only signed up with Social login needs to register a Password by using the Password reset flow.
User-facing flows with social identity providers
During signup with social identity providers, the user may be prompted to allow Identity Cloud to use their information from the social identity provider. Denying access to the information terminates the signup flow.